ブランチの権限
ブランチ権限は、特定のワークフローを強制し、ワークスペースの新しいメンバーが master を削除してしまうようなエラーを防ぐために役立ちます。
ブランチ権限でできること:
- 任意のブランチに書き込みまたはマージできるユーザー/グループを厳密にコントロールします。
- 特定のブランチ タイプやパターンに対応する権限を作成します。たとえば、
/PROJECT-*は、PROJECT-1234などの名前を持つすべてのブランチへのアクセスを制限します。
ワークスペースのワークフローをさらに厳密に管理したい場合はマージ チェックについて確認してください。マージ チェックでは、個別のブランチやブランチ パターンのマージについて、特定の条件を推奨または要求することができます。マージ チェックについて詳細を読む。
Merge checks are a Premium feature for Bitbucket Cloud. Learn more about Bitbucket Premium.
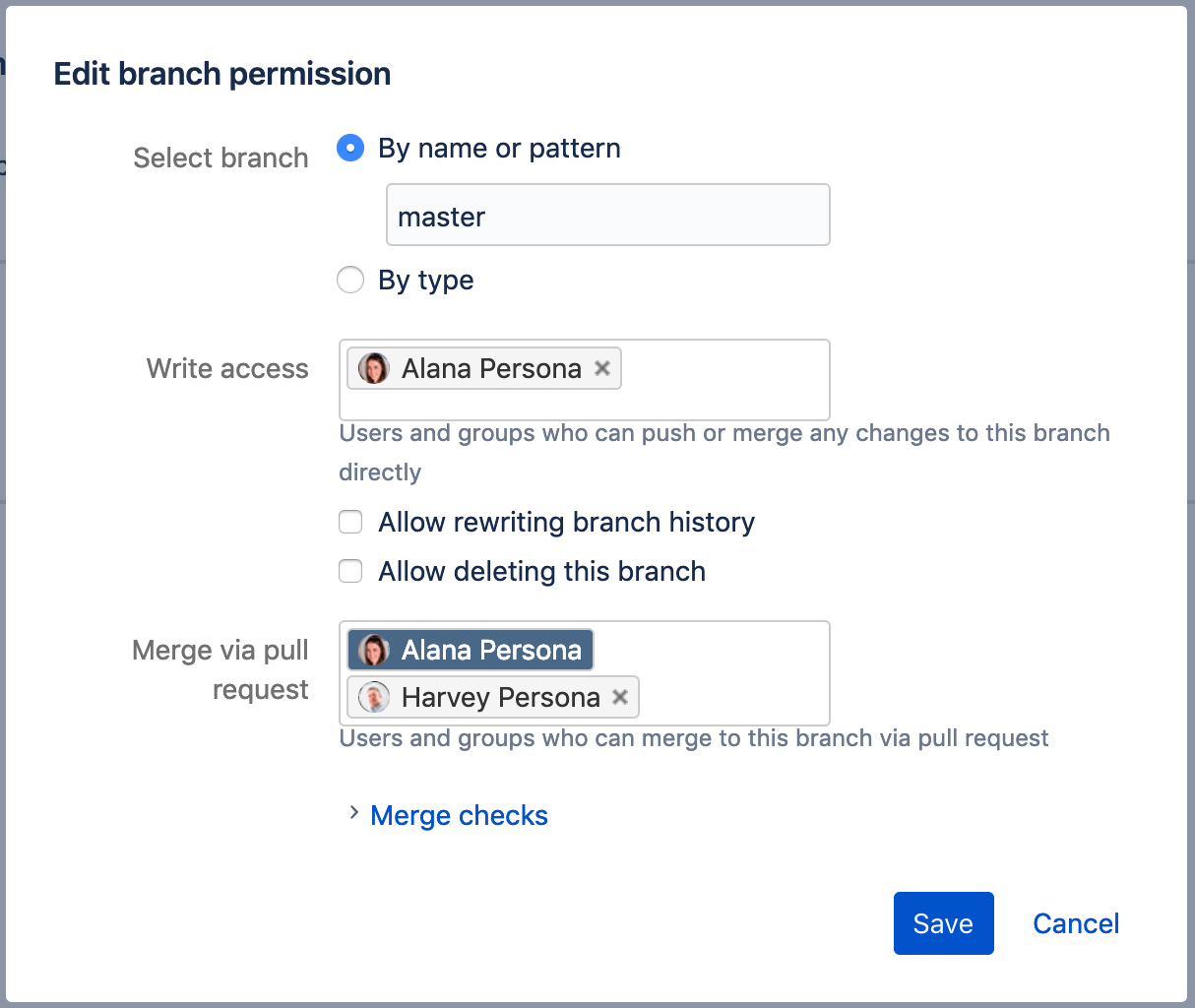
権限のセットアップの例
たとえば、Alana (主任エンジニア)、Harvey (QA リーダー)、およびその他の 5 人のエンジニアが Teams in space プロジェクトに携わっているとします。効果的に作業できるよう、全員がリポジトリへの書き込みアクセス権を持っています。今回は、リポジトリの master ブランチと develop ブランチへのアクセスを管理する必要があります。次のように権限を割り当てます。
- Alana にのみ master への直接書き込みを許可
- Alana と Harvey にのみ master へのマージを許可
- 全員に develop へのマージを許可 (ただしプルリクエスト経由でのみ)
Branch types
ブランチ モデル を有効にしている場合、特定のタイプのすべてのブランチに対するアクセス権限を構成できます。これは、たとえば、すべてのリリース ブランチでマージ アクセスを制限したい場合などに便利です。
ブランチ パターン
タイプよりもさらに細かくする必要がある場合は、文字列のいずれかの端にワイルドカード文字 (*) を追加することで、特定のパターンのブランチ名 (PROJECT- など) に対する権限を設定することもできます。例:
PROJECT-*: "PROJECT-*" という名前のブランチと一致します (名前空間を含む)。したがって、制限は次のようなブランチに適用されます。
PROJECT-1234
PROJECT-new
PROJECT-1.1
ブランチ権限の重複
誤ってブランチ権限が重複してしまうことがあります。たとえば、ブランチ名 master 専用のブランチ権限を作成し、ブランチ パターン * を使用した権限も作成した場合、master ブランチには両方の権限が適用されます。
次の表に、権限定義が重複した場合の結果の例を示します。
| ワイルドカード (*) ブランチ パターン | 特定の ("master") ブランチ名 | 両方の制限に含まれるブランチに適用される制限 |
|---|---|---|
| ユーザーまたはグループ制限 (書き込みまたはマージ アクセス) | ||
| ユーザーまたはグループがリストされていない | Alana | Alana のみがアクセス権を保持 |
| 全員 | Alana | Alana のみがアクセス権を保持 |
| Alana | Harvey | Alana と Harvey の両方がアクセス権を保持 |
| Alana | ユーザーまたはグループがない | Alana のみがアクセス権を保持 |
| Alana | 全員 | Alana のみがアクセス権を保持 |