Apache HTTP Server (mod_proxy_http) でアトラシアンのサーバー アプリケーションをプロキシする
プラットフォームについて: Server および Data Center のみ。この記事は、Server および Data Center プラットフォームのアトラシアン製品にのみ適用されます。
Support for Server* products ended on February 15th 2024. If you are running a Server product, you can visit the Atlassian Server end of support announcement to review your migration options.
*Fisheye および Crucible は除く
Atlassian applications allow the use of reverse-proxies with our products; however, Atlassian Support does not provide assistance for configuring them. Consequently, Atlassian cannot guarantee providing any support for them.
設定でサポートが必要な場合、アトラシアン コミュニティに質問を登録してください。
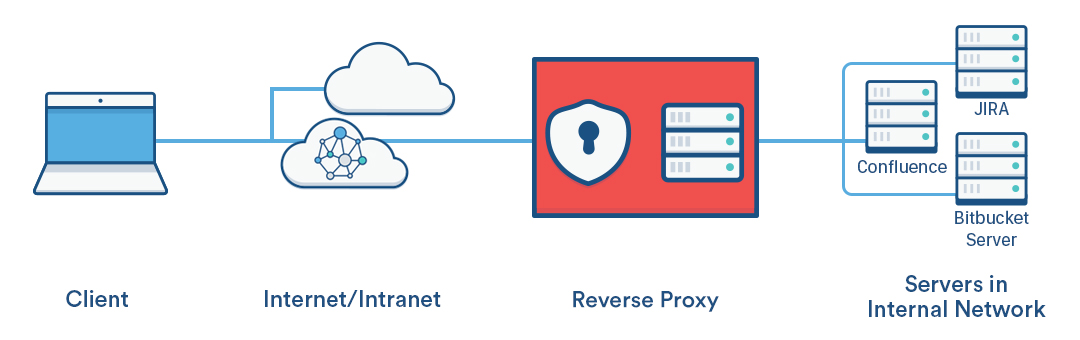
このページでは、Apache HTTP Server がアトラシアンのサーバー アプリケーションのリバース プロキシとして動作するネットワーク トポロジを確立する方法を説明します。 このページの手順に厳密に従って設定を行うことをおすすめします。
アトラシアン アプリケーションでのリバース プロキシの使用は、ユーザーに次のようなアクセス方法を提供したいときに検討します。
- 自身のドメインでのアクセス (例:
http://my<atlassianapp>.com/) - 他のドメインのサブドメインでのアクセス (例:
http://my<atlassianapp>.ourcompany.com/) - ドメインまたはサブドメインのコンテキスト パスでのアクセス (例:
http://ourcompany.com/my<atlassianapp>) - 異なる HTTP ポート (例: 9800、9850 など)
より複雑なシナリオについては、Apache HTTP Server のドキュメント を参照したり、ご自身の組織内の Apache 担当者に相談したり、Attlasian Answers で質問したり、アトラシアン エキスパートを利用したりしていただくことをおすすめします。
このページの手順は、アトラシアンの次のサーバー アプリケーションに適用されます。
- Jira Server アプリケーション (Jira Software Server、Jira Core、Jira Service Desk)
- Confluence Server (このガイドでは Confluence 6.0 以降向けの追加手順も案内しています)
- Bamboo Server
- Bitbucket Server
- Fisheye
- Crucible
- Crowd
In the examples that follow on this page, <atlassianapp> refers to the name of any of the Atlassian server applications above.
アトラシアンのサーバー アプリケーションには web サーバーが同梱されるため、製品をプロキシ サーバーなしで実行できます。web サーバーとして、ほとんどのアトラシアン アプリケーションに Apache Tomcat が同梱されます (Fisheye と Crucible は Jetty を使用します)。このため、アトラシアン アプリケーションをプロキシする再は、Tomcat (Fisheye または Crucible を使用している場合は Jetty) と Apache HTTP Server の両方を設定する必要があります。
For HTTPS conections, refer to Securing your Atlassian applications with Apache using SSL.
Prerequisites
次の条件を満たしている必要があります。
Apache バージョン 2.2 または 2.4 がインストール済み
httpd.conf ファイルを編集して Apache HTTP Server を設定する方法については、Apache HTTP Server のドキュメントをご参照ください。特に「Apache Module mod_proxy」セクションが有用です。httpd.conf ファイルへの変更は、Apache HTTP Server の再起動後にのみ有効になることにご注意ください (Confluence 6.0 などの、Synchrony を使用するアプリケーションは Apache 2.4.10 以降を使用する必要があります)。
ドメインの DNS エントリが配置および設定済み
セットアップするプロキシ トポロジに応じた変更が組織の現在の DNS 設定に必要かどうかを、必要に応じてシステムまたはネットワーク管理者とともに確認します。
アトラシアン アプリケーションがインストール済みで、Web ブラウザからアクセス可能
アトラシアン アプリケーションを通常の手順でインストールします。
パート A. アトラシアン アプリケーションを設定する
このセクションでは、各アトラシアン アプリケーションに同梱の Tomcat (または Jetty) Web サーバーをリバース プロキシの背後で実行するように設定する方法について説明します。
1. アトラシアン アプリケーションを停止する
アプリケーションを停止すると、Tomcat も停止します。
2. コンテキスト パスを設定する
このステップは、アプリケーションへのアクセスを http://ourcompany.com/<contextpath> などのコンテキスト パス上で行いたい場合にのみ必要です。不要な場合は、このステップをスキップできます。
Fisheye および Crucible
FishEye または Crucible をプロキシする場合、管理領域から Jetty の Web コンテキスト パスを設定します。「Fisheye の web サーバーを設定する」を参照してください。
Jira アプリケーション、Confluence、Bitbucket Server、Bamboo
これらのアトラシアンのサーバー アプリケーションのいずれかをプロキシする場合、Tomcat の server.xml ファイルでコンテキスト パスを次のように設定します。
Bitbucket Server 5.0 を構成している場合
Bitbucket Server 5.0 以降では Tomcat のコネクタを直接設定することができません。このため、このセクションの設定は、Bitbucket Server 4.14 以前でのみ利用できます。
server.xml の設定は、<Bitbucket home directory>/shared/bitbucket.properties で置き換えられています。
Please read through Change Bitbucket's context path for Bitbucket Server 5.0 and later specific instructions.
Tomcat の server.xml 設定ファイルには、次のような Context ディレクティブがあります (Crowd を除く)。
<Context path="" docBase="${catalina.home}/atlassian-<atlassianapp>" reloadable="false" useHttpOnly="true">ディレクティブを変更して、新しいコンテキスト パスを追加します。
<Context path="/<contextpath>" docBase="${catalina.home}/atlassian-<atlassianapp>" reloadable="false" useHttpOnly="true"><contextpath> には独自の値を使用します。一般に、各アプリケーションで異なるコンテキスト パスを使用します。
path の値の先頭では path="<contextpath>" ではなく path="/<contextpath>" のように、スラッシュ (/) が必要です。
Use these instructions to Removing the 'crowd' Context from the Application URL.
3. Connector ディレクティブを設定する
FishEye または Crucible を使用している場合、管理領域からプロキシ ホスト、プロキシ スキーム、およびプロキシ ポートを設定します。詳細については、「Fisheye web サーバーを設定する」を参照してください。
Bitbucket Server 5.0 を構成している場合
Bitbucket Server 5.0 以降では Tomcat のコネクタを直接設定することができません。このため、このセクションの設定は、Bitbucket Server 4.14 以前でのみ利用できます。
server.xml の設定は、<Bitbucket home directory>/shared/bitbucket.properties で置き換えられています。
対応するプロパティと、以降の設定に対応する手順については、「server.xml のカスタマイズを bitbucket.properties に移行する」をご参照ください。bitbucket.properties へのマッピングが完了したら、「パート B: Apache HTTP Server を設定する」に進んでください。
その他のアトラシアン サーバー アプリケーションのいずれかを使用している場合、Connector ディレクティブを次のように設定します。
For each application, find the normal (non-SSL) Connector directive in the Tomcat <jira-install>/conf/server.xml file, and add the scheme, proxyName, and proxyPort attributes inside the Connector directive, as below. Use the default values for the other attributes, including for port , unless you have a particular reason to change them, and use your own domain name for the proxyName value:
<Connector port=<default>
maxThreads=<default>
minSpareThreads=<default>
connectionTimeout=<default>
enableLookups=<default>
maxHttpHeaderSize=<default>
protocol=<default>
useBodyEncodingForURI=<default>
redirectPort=<default>
acceptCount=<default>
disableUploadTimeout=<default>
proxyName="<subdomain>.<domain>.com"
proxyPort="80"
scheme="http"/>proxyName パラメータは、Apache HTTP Server のサービス提供元として設定する FQDN に設定する必要があることにご注意してください。これは、ユーザーがアプリケーションにアクセスするためにブラウザに入力するアドレスです。 例:
http://<atlassianapp>.ourcompany.comなどのサブドメインでアプリケーションにアクセスする場合:<atlassianapp>.ourcompany.comhttp://ourcompany.com/<atlassianapp>などのコンテキスト パスでアプリケーションにアクセスする場合:ourcompany.com。この場合、コンテキスト パスをproxyNameパラメータに含めず、上述のステップ 2 でContextディレクティブを設定済みである必要があります。
For more information about configuring the Tomcat Connector, refer to the Apache Tomcat 7.0 HTTP Connector Reference.
パート B. Apache HTTP Server を設定する
アトラシアンでは、mod_proxy モジュールを使用することを推奨しています。このモジュールは、 Apache のプロキシ、ゲートウェイ、またはキャッシュを実装し、さらに、単一のクライアントで複数の仮想ホストを有効化します。
mod_proxy プロキシの詳細については、次のページをご参照ください。
- mod_proxy_html サイトには、ドキュメントや複数のサンプルがあります。
- Apache Week チュートリアルは、2 つのアプリケーションと ProxyHTMLURLMap を持つ複雑な状況について説明しています。
1. Apache で mod_proxy モジュールを有効化する
必要に応じて、必要なモジュールを Apache で次のように有効化します。
2. mod_proxy を使用して仮想ホストを設定する
Apache のリバース プロキシの背後で 1 つのアトラシアン アプリケーションを実行している場合、次のディレクティブで仮想ホスト ブロックを使用します。
<VirtualHost *:80>
ServerName <subdomain>.<domain>.com
ProxyRequests Off
ProxyVia Off
<Proxy *>
Require all granted
</Proxy>
ProxyPass /<contextpath> http://<internal_domain>:<port>/<contextpath>
ProxyPassReverse /<contextpath> http://<internal_domain>:<port>/<contextpath>
</VirtualHost>- CentOS の場合、
/etc/httpd/conf.d/で各アプリケーションに対応する個別の設定ファイルに仮想ホスト ブロックを追加する (例:confluence-vhost.conf、jira-vhost.conf) 手法が推奨されていることにご注意ください。 - Debian の場合、
/etc/apache2/sites-available/<site>で各アプリケーションに対応する個別の設定ファイルに仮想ホスト ブロックを追加する (例:confluence.conf、jira.conf) 手法が推奨されていることにご注意ください。これらは既定テンプレートである000-default.confに基づいている必要があります。
ProxyPass および ProxyPassReverse ディレクティブでは、末尾にスラッシュを追加する必要がある場合があります。例:
ProxyPass /<contextpath> http://<internal_domain>:<port>/<contextpath>/ ProxyPassReverse /<contextpath> http://<internal_domain>:<port>/<contextpath>/
末尾のスラッシュは、スラッシュが不足していることによる DNS エラーが Apache のログ ファイルで確認されている場合にのみ使用します。この問題の詳細や、解決方法についての追加情報について、こちらのサードパーティ ブログで説明されています。ほとんどの場合、この操作は不要です。
1 つのプロキシの背後で複数のアプリケーションを実行している場合、名前ベースの仮想ホストを使用できます。
アトラシアン アプリケーションが同じドメインで異なるコンテキスト パスで実行されている場合は、名前ベースの仮想ホストを 1 つ使用します。例:
<VirtualHost *:80> ServerName mycompany.com ProxyRequests Off ProxyVia Off <Proxy "*"> Require all granted </Proxy> ProxyPass /jira http://<internal_domain>:8080/jira ProxyPassReverse /jira http://<internal_domain>:8080/jira ProxyPass /bitbucket http://<internal_domain>:7990/bitbucket ProxyPassReverse /bitbucket http://<internal_domain>:7990/bitbucket </VirtualHost>各アプリケーションが異なるドメインにある場合は、名前ベースの仮想ホストを複数使用します。例:
<VirtualHost *:80> ServerName myjira.com ProxyRequests Off ProxyVia Off <Proxy *> Require all granted </Proxy> ProxyPass /jira http://<internal_domain>:8080/jira ProxyPassReverse /jira http://<internal_domain>:8080/jira </VirtualHost> <VirtualHost *:80> ServerName mybitbucket.com ProxyRequests Off ProxyVia Off <Proxy *> Require all granted </Proxy> ProxyPass /bitbucket http://<internal_domain>:7990/bitbucket ProxyPassReverse /bitbucket http://<internal_domain>:7990/bitbucket </VirtualHost>
Confluence 6.0 以降を Synchrony (共同編集に必要) と使用している場合、Apache 2.4.10 以降を使用する必要があります。
仮想ホストの設定や各ディレクティブの使用方法の完全な詳細情報については、https://httpd.apache.org/docs/2.4/vhosts/ をご参照ください。
3. Apache を再起動する
Debian および Ubuntu
以下を使用して、コマンド ラインから Apache を再起動します。
$ sudo service apache2 restartFedora および CentOS
以下を使用して、コマンド ラインから Apache を再起動します。
$ sudo apachectl gracefulsystemd を使用して Apache を再起動することもできます。CentOS の場合の例は次のようになります。
$ sudo systemctl restart httpd.serviceWindows
Apache サービスを停止および開始するには、[コントロール パネル] > [管理ツール] > [サービス] に移動し、"Apache2" を見つけ、それを選択します。メニュー バーから停止ボタン (四角形) を選択し、サービスのステータスが [停止] になるまで待ちます。サービスが停止したら、開始ボタン (三角形) を選択し、ステータスが [開始] になるまで待ちます。
4. CentOS の SELinux ポリシーを変更する
CentOS では、httpd のネットワークへの接続を SELinux ポリシーが既定でブロックします。この場合、httpd error_log に次のような "permission denied" メッセージが表示されます。
[Sat Mar 19 00:29:45.722758 2016] [proxy:error] [pid 5958] (13)Permission denied: AH00957: HTTP: attempt to connect to 127.0.0.1:8090 (localhost) failed次のコマンドを使用して、httpd プロセスについての SELinux ポリシーを手動で変更する必要があります。
$ sudo /usr/sbin/setsebool -P httpd_can_network_connect 1
5. X-Forwarded-For ヘッダーを有効にする
これは、プロキシ IP ではなく origin IP (プロキシに接続しているユーザー) をアトラシアン アプリケーションに送信するようにするための、オプションのステップです。この設定は、リクエストを送信しているユーザーの追跡に役立ちます。設定を行わない場合、リバース プロキシによってユーザーの IP がマスクされる可能性があります。この変更を行うと、アクセス ログにはプロキシだけではなく、クライアントの IP がプロキシとともに記録されます。これを実現するには、次の手順を実行します。
mod_remoteipモジュールを有効化します。以下を適切な仮想ホストに追加します。
RemoteIPHeader X-Forwarded-For- Apache を再起動またはリロードします。
パート C. 最終設定
各アプリケーションを再起動する
各アプリケーションを再起動し、新しい URL を使用してアクセスできることを確認します。 上述の停止と開始についての手順をご確認ください。
アプリケーションのベース URL を設定する
各アトラシアン アプリケーションで、プロキシで構成したアドレスをベース URL として設定します。これは Apache HTTP Server が提供する URL です (例: http://www.example.com/<atlassianapp >)。
HTTP 圧縮を無効にする
プロキシと Tomcat の両方で圧縮を実行すると、アトラシアン アプリケーションを別のアトラシアン アプリケーションと連携する際に問題が発生することがあります。Jira アプリケーションと Confluence では HTTP 圧縮を無効にすることを推奨しています。
- Jira アプリケーション - 「Jira アプリケーションのオプションの設定」を参照
- Confluence – 「Confluence 内で HTTP レスポンスを圧縮する」を参照